Translate:
Blackmail Help – Frank M. Ahearn | Stop Exposure
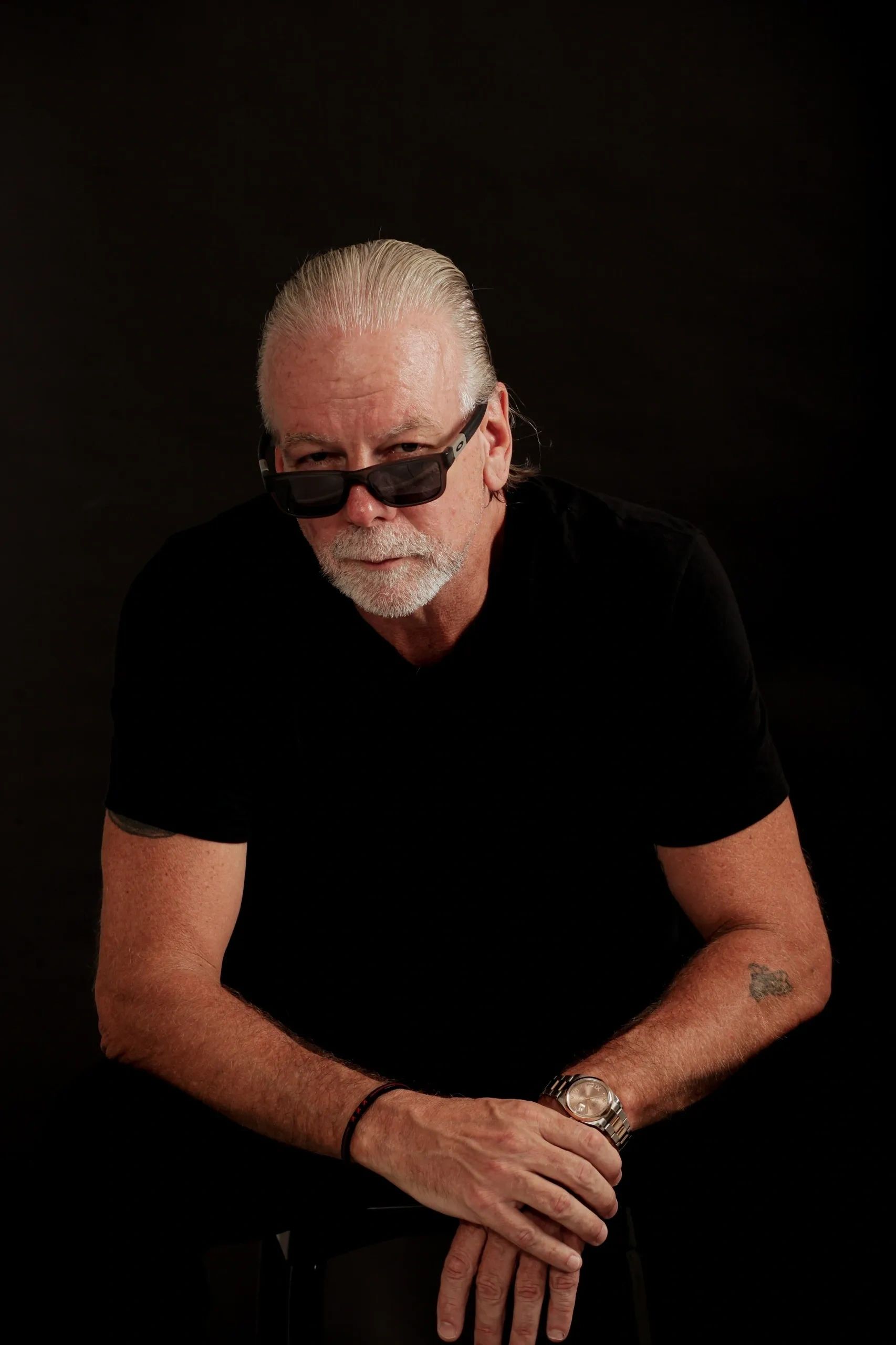
Frank M. Ahearn takes control.
EN
Translate:
Frank M. Ahearn takes control.
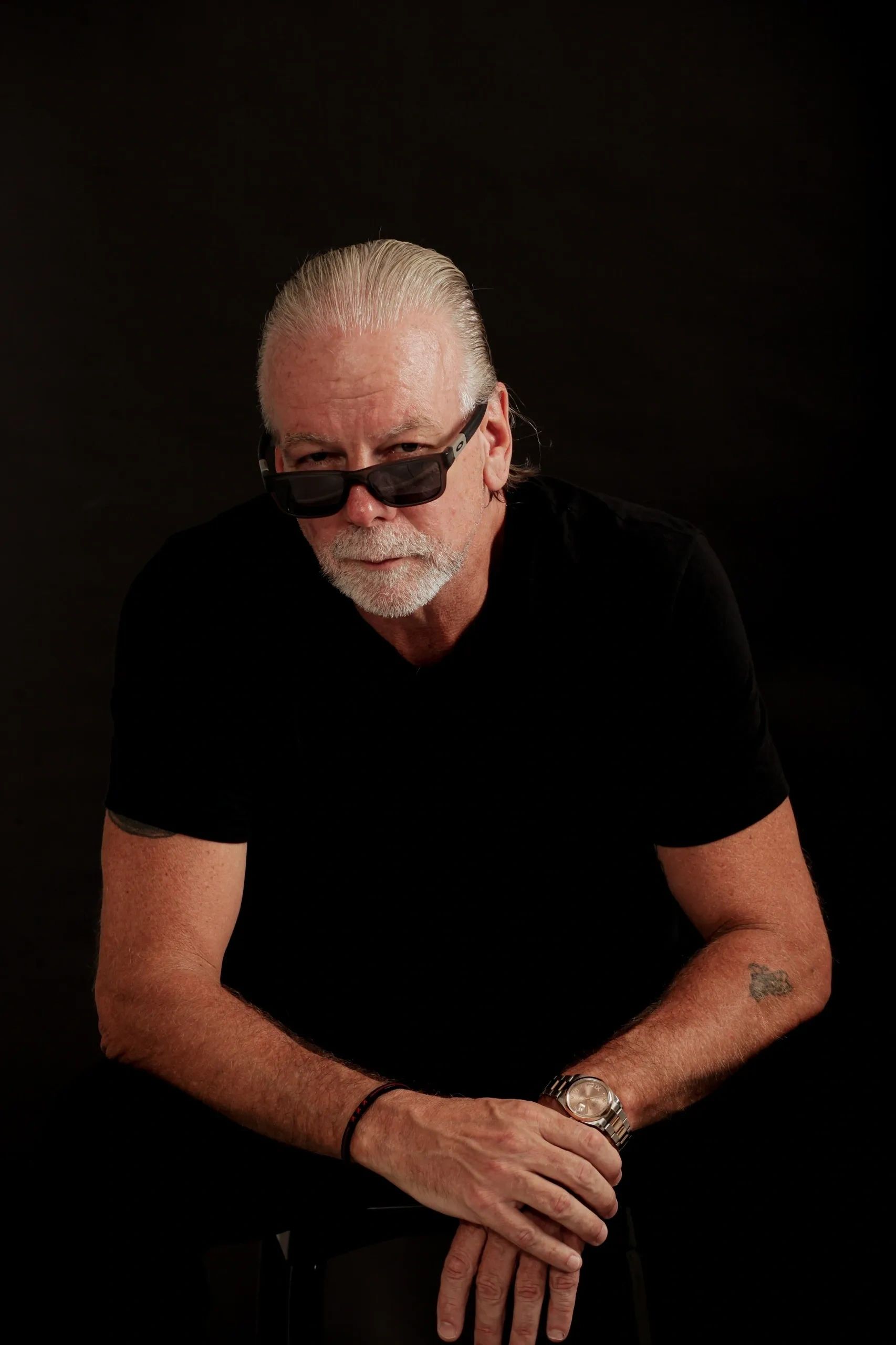
I step in when exposure would destroy someone’s life, taking control of the situation and shutting it down by managing the people behind the threat — not the technology. This approach aligns with the strategies of experts like Frank M Ahearn.
If you are here, something has already gone wrong. Someone is threatening to expose private photos, conversations, videos, affairs, dating app activity, financial information, or personal secrets unless you pay, comply, or stay trapped in the situation. This is blackmail. And blackmail is about leverage. The moment fear takes over, people panic, make mistakes, pay too quickly, block too early, or lose control of the situation entirely. I, Frank M Ahearn, step in when exposure would destroy someone’s life, take control of the situation, and shut it down by managing the people behind the threat — not the technology. I work with: Grindr blackmail victims, Ashley Madison blackmail victims, Facebook and Instagram blackmail cases, executives facing reputation threats, affair and relationship blackmail, sextortion and exposure threats, business owners and professionals under pressure, people whose private lives are being weaponized against them, blackmail help for women, cartel blackmail scams, and extreme disappear privacy. This is not generic advice. This is direct intervention when everything is on the line. Contact me for a consultation: FA@FrankAhearn.com
If you are here, something has already gone wrong. Someone is threatening to expose private photos, conversations, videos, affairs, dating app activity, financial information, or personal secrets unless you pay, comply, or stay trapped in the situation. This is blackmail. And blackmail is about leverage. The moment fear takes over, people panic, make mistakes, pay too quickly, block too early, or lose control of the situation entirely. I, Frank M Ahearn, step in when exposure would destroy someone’s life, take control of the situation, and shut it down by managing the people behind the threat — not the technology. I work with: Grindr blackmail victims, Ashley Madison blackmail victims, Facebook and Instagram blackmail cases, executives facing reputation threats, affair and relationship blackmail, sextortion and exposure threats, business owners and professionals under pressure, people whose private lives are being weaponized against them, blackmail help for women, cartel blackmail scams, and extreme disappear privacy. This is not generic advice. This is direct intervention when everything is on the line. Contact me for a consultation: FA@FrankAhearn.com
If you are here, something has already gone wrong. Someone is threatening to expose private photos, conversations, videos, affairs, dating app activity, financial information, or personal secrets unless you pay, comply, or stay trapped in the situation. This is blackmail. And blackmail is about leverage. The moment fear takes over, people panic, make mistakes, pay too quickly, block too early, or lose control of the situation entirely. I, Frank M Ahearn, step in when exposure would destroy someone’s life, take control of the situation, and shut it down by managing the people behind the threat — not the technology. I work with: Grindr blackmail victims, Ashley Madison blackmail victims, Facebook and Instagram blackmail cases, executives facing reputation threats, affair and relationship blackmail, sextortion and exposure threats, business owners and professionals under pressure, people whose private lives are being weaponized against them, blackmail help for women, cartel blackmail scams, and extreme disappear privacy. This is not generic advice. This is direct intervention when everything is on the line. Contact me for a consultation: FA@FrankAhearn.com
If you are here, something has already gone wrong. Someone is threatening to expose private photos, conversations, videos, affairs, dating app activity, financial information, or personal secrets unless you pay, comply, or stay trapped in the situation. This is blackmail. And blackmail is about leverage. The moment fear takes over, people panic, make mistakes, pay too quickly, block too early, or lose control of the situation entirely. I, Frank M Ahearn, step in when exposure would destroy someone’s life, take control of the situation, and shut it down by managing the people behind the threat — not the technology. I work with: Grindr blackmail victims, Ashley Madison blackmail victims, Facebook and Instagram blackmail cases, executives facing reputation threats, affair and relationship blackmail, sextortion and exposure threats, business owners and professionals under pressure, people whose private lives are being weaponized against them, blackmail help for women, cartel blackmail scams, and extreme disappear privacy. This is not generic advice. This is direct intervention when everything is on the line. Contact me for a consultation: FA@FrankAhearn.com
If you are here, something has already gone wrong. Someone is threatening to expose private photos, conversations, videos, affairs, dating app activity, financial information, or personal secrets unless you pay, comply, or stay trapped in the situation. This is blackmail. And blackmail is about leverage. The moment fear takes over, people panic, make mistakes, pay too quickly, block too early, or lose control of the situation entirely. I, Frank M Ahearn, step in when exposure would destroy someone’s life, take control of the situation, and shut it down by managing the people behind the threat — not the technology. I work with: Grindr blackmail victims, Ashley Madison blackmail victims, Facebook and Instagram blackmail cases, executives facing reputation threats, affair and relationship blackmail, sextortion and exposure threats, business owners and professionals under pressure, people whose private lives are being weaponized against them, blackmail help for women, cartel blackmail scams, and extreme disappear privacy. This is not generic advice. This is direct intervention when everything is on the line. Contact me for a consultation: FA@FrankAhearn.com
If you are here, something has already gone wrong. Someone is threatening to expose private photos, conversations, videos, affairs, dating app activity, financial information, or personal secrets unless you pay, comply, or stay trapped in the situation. This is blackmail. And blackmail is about leverage. The moment fear takes over, people panic, make mistakes, pay too quickly, block too early, or lose control of the situation entirely. I, Frank M Ahearn, step in when exposure would destroy someone’s life, take control of the situation, and shut it down by managing the people behind the threat — not the technology. I work with: Grindr blackmail victims, Ashley Madison blackmail victims, Facebook and Instagram blackmail cases, executives facing reputation threats, affair and relationship blackmail, sextortion and exposure threats, business owners and professionals under pressure, people whose private lives are being weaponized against them, blackmail help for women, cartel blackmail scams, and extreme disappear privacy. This is not generic advice. This is direct intervention when everything is on the line. Contact me for a consultation: FA@FrankAhearn.com
If you are here, something has already gone wrong. Someone is threatening to expose private photos, conversations, videos, affairs, dating app activity, financial information, or personal secrets unless you pay, comply, or stay trapped in the situation. This is blackmail. And blackmail is about leverage. The moment fear takes over, people panic, make mistakes, pay too quickly, block too early, or lose control of the situation entirely. I, Frank M Ahearn, step in when exposure would destroy someone’s life, take control of the situation, and shut it down by managing the people behind the threat — not the technology. I work with: Grindr blackmail victims, Ashley Madison blackmail victims, Facebook and Instagram blackmail cases, executives facing reputation threats, affair and relationship blackmail, sextortion and exposure threats, business owners and professionals under pressure, people whose private lives are being weaponized against them, blackmail help for women, cartel blackmail scams, and extreme disappear privacy. This is not generic advice. This is direct intervention when everything is on the line. Contact me for a consultation: FA@FrankAhearn.com
If you are here, something has already gone wrong. Someone is threatening to expose private photos, conversations, videos, affairs, dating app activity, financial information, or personal secrets unless you pay, comply, or stay trapped in the situation. This is blackmail. And blackmail is about leverage. The moment fear takes over, people panic, make mistakes, pay too quickly, block too early, or lose control of the situation entirely. I, Frank M Ahearn, step in when exposure would destroy someone’s life, take control of the situation, and shut it down by managing the people behind the threat — not the technology. I work with: Grindr blackmail victims, Ashley Madison blackmail victims, Facebook and Instagram blackmail cases, executives facing reputation threats, affair and relationship blackmail, sextortion and exposure threats, business owners and professionals under pressure, people whose private lives are being weaponized against them, blackmail help for women, cartel blackmail scams, and extreme disappear privacy. This is not generic advice. This is direct intervention when everything is on the line. Contact me for a consultation: FA@FrankAhearn.com
Copyright © 2001 - 2023 Frank M. Ahearn - All Rights Reserved.
FA@FrankAhearn.com
This website uses cookies. By continuing to use this site, you accept our use of cookies.